How Much Of Chinese 5G Technology Is Still Used In Europe? – Analysis
By Miguel Otero Iglesias*
For many years European telecom operators have used Chinese 3G and 4G technology from vendors such as Huawei and ZTE. The issue was a no-brainer. China was not seen as a national security threat –in fact, the EU had signed a comprehensive strategic partnership with China in 2003– and Chinese technology was cheaper and, for many tech experts, even better than that of European vendors like Ericsson and Nokia. Hence, many European telecoms signed strategic partnerships with their Chinese providers and used their technology both in Europe and in their overseas businesses in the Global South.
But along came Trump with his aggressive policy against Huawei and ZTE, and everything changed. In the US, Chinese 5G technology was banned and many close allies followed suit, especially Japan and the other Five Eyes Countries, first Australia and New Zealand, and more recently the UK and Canada. In Europe there was at first some resistance to US pressure to exclude Chinese 5G technology. It could even be argued, back in 2018, that the intense diplomacy exerted by US embassies in many European capitals was counter-productive, as it triggered a backlash. Many pointed out that the Wikileaks wires showed that it was the US which was spying on Europe, not China.
There was no concrete evidence that China was using backdoors in the 4G technology deployed in Europe, so why would it do so in 5G? The cyber-intelligence community was also sending mixed messages. Some said that the risks of espionage and sabotage were manageable, while other qualified sources pointed to potential disruptions and threats to national security.
By 2019, however, the debate was tilting towards the increased ‘threat’ side. October of that year saw the publication of an EU-wide coordinated risk assessment report on cybersecurity of 5G networks by its member states. There one could read the following:
‘Threats posed by States or State-backed actors, are perceived to be of highest relevance. They represent indeed the most serious as well as the most likely threat actors, as they can have the motivation, intent and most importantly the capability to conduct persistent and sophisticated attacks on the security of 5G networks.’
There is no doubt that by ‘States and state-backed actors’ the drafters were mostly thinking of Russia and China, but especially the latter, given its advances in 5G technology. Not long after, in January 2020, the European Council approved the EU Cybersecurity Toolbox of risk-mitigating measures in 5G technology. The wording here is also telling:
‘Threats to availability and integrity of networks will become major security concerns: in addition to confidentiality and privacy threats, with 5G networks expected to become the backbone of many critical IT applications, the integrity and availability of those networks will become major national security concerns and a major security challenge from an EU perspective.’
Member states were given some time to incorporate the new 5G toolbox to their national legislation, and many did so by introducing new Cybersecurity laws. But two years later, in October of 2022, the European Commission sent a recommendation to the Council urging certain member states to implement the toolbox effectively. Again, the specific paragraph said:
‘Member States should urgently achieve the implementation of the measures recommended in the EU Toolbox on 5G Cybersecurity. Member States which have not yet enacted restrictions on high-risk suppliers should do so without further delay, considering that time lost can increase vulnerability of networks in the Union.’
Given this context, the question that remains is: how much of Chinese 4G/5G technology is still used in the EU? The answer is not easy. Many telecom companies are not completely transparent in this regard, although John Strand and his team at Strand Consult have come up with very interesting research in this area. They are a big consulting firm for telecom operators and therefore have access to the relevant data. Their first big find is that there is now a strong consensus in Europe to move away from Chinese 5G technology in the ‘core’ of the networks. Almost all operators have replaced Huawei or are bound to do so.
However, Strand, like many other experts, does not think that it is smart to separate the ‘core’ from the ‘periphery’ in 5G because as software is increasingly used in all parts of the network and the tendency is to undertake ‘core’ operations closer to the end-user to reduce latency, the security risks obvious in the ‘core’ (the brain of the network) extend to the so-called periphery. Therefore, John Strand and his team focus their attention on how much Chinese technology is used in the Radio Access Network (RAN), traditionally called ‘the periphery’, as a proxy for potential risks.
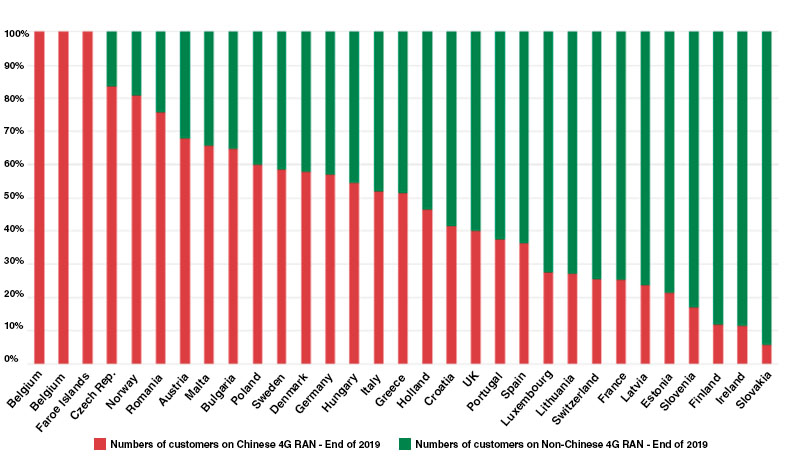
They have looked at RAN technology in 4G of 102 telecom operators in Europe and the results are quite interesting (see Figure 1).
Figure 1: Telecom Customers on Chinese vs non-Chinese 4G RAN
As of the end of 2019 there were three countries in Europe which operated with 100% Chinese 4G RAN technology. Shockingly, this includes Belgium, the host country of most EU institutions. At the other extreme, countries like Slovakia, Ireland and Finland had very little exposure to Chinese tech. Of the big countries, Germany was the one that used more Chinese 4G technology, at 57%, with Italy second, at 52%. The Netherlands is at 47% and Spain at 36%. France, by contrast, is the most decoupled from the big countries, with only 25% Chinese 4G RAN equipment.
John Strand and his team have even disaggregated numbers for every single telecom company (see Figure 2).
Figure 2: Share of Chinese 4G RAN – Group Level
| Operator Group | Share of Chinese 4G RAN |
|---|---|
| Proximus | 100,00% |
| United Group | 100,00% |
| GTAM | 100,00% |
| Liberty Global | 100,00% |
| Sunrise | 100,00% |
| TDC | 100,00% |
| Monaco Telecom | 100,00% |
| 4ka | 100,00% |
| Telemach | 100,00% |
| Melita | 100,00% |
| Primetel | 100,00% |
| FT | 100,00% |
| Kall | 100,00% |
| P4 | 90% |
| PPF | 74,23% |
| BT | 65,00% |
| Vodafone | 61,55% |
| Hutchison | 58,14% |
| Deutsche Telekom | 57,34% |
| Telenor | 55,86% |
| TIM | 55,00% |
| Altice | 55,00% |
| Tele2 | 54,17% |
| Bouygues | 50,00% |
| NOS | 50,00% |
| Eir | 50,00% |
| Orange | 47,64% |
| RCS&RDS | 46,25% |
| Elisa | 34,28% |
| Bite | 32,60% |
| Telefonica | 25,08% |
| Telia | 18,95% |
| Ice | 0,00% |
| Iliad | 0,00% |
| KPN | 0,00% |
| Masmovil | 0,00% |
| Polkomtel | 0,00% |
| Post | 0,00% |
| Swisscomm | 0,00% |
| T-2 | 0,00% |
| Telekom Austria | 0,00% |
| Telekom Slovenije | 0,00% |
| Tunisie Telecom | 0,00% |
Here it needs to be highlighted that the big operators using more Chinese equipment are BT, Vodafone and Deutsche Telekom, while Orange and Telefónica have lower figures. At the extremes there are companies like Proximus in Belgium, with 100% Chinese RAN technology, while Telekom Austria uses 0%.
The reader might now object and say: ‘Yes, but this is 4G RAN technology and in 2019. What about 5G RAN technology and in 2022?’. Fortunately, Strand Consult is about to release these numbers over the following weeks, and I had the chance of talking to John Strand himself regarding the results of this new investigation. According to Strand, the numbers should be fairly similar, especially for the bigger countries, with Germany having an exposure of close to 60%, making it quite vulnerable. But there are two exceptions: Norway and Belgium, which have drastically lowered their dependence on Chinese RAN technology in 5G.
Hence, it seems that the EU as a whole is taking the issue seriously. Excluding Chinese tech from the ‘core’ is a big step, but the substitution of Chinese RAN technology is a slower process, especially in the bigger countries. What are the risks involved? John Strand is very bold in denouncing the risks. The Chinese state can use its technology to hoover data back to China, thus benefiting Chinese companies and the CCP, and it can also switch off its technology should it desire to, thereby leaving countries like Germany in the dark.
I am not sure whether this is so clear cut. If Huawei and ZTE send private data from European customers back to China, I imagine that the European cyber-intelligence community would notice and enforce wholesale bans. The reputation of the Chinese vendors would be destroyed. This has not happened yet. Furthermore, I do not know whether Chinese companies, or the CCP for that matter, have a ‘big switch’ to stop the use of 5G technology abruptly. If so, a diversification strategy of vendors would be necessary, and yes, one should call for the banning of high-risk vendors.
Finally, another question remains. Even if we use only 5G, or 6G, technology from trusted vendors, how safe are we really? Can Chinese operators penetrate our own networks and still do the espionage and sabotage that we so fear? If so, what other measures need to be deployed? And should we not think of being able to penetrate Chinese networks too? If China can collect our data, perhaps we should think of ways of collecting data produced in China as well (perhaps we are doing so already). Nevertheless, these are all open questions from a non-expert on this subject.
*About the author: Miguel Otero-Iglesias is Senior Analyst at the Elcano Royal Institute and Professor at IE School of Global and Public Affairs. He is also Research Associate at the EU-Asia Institute at ESSCA School of Management in France. Previously he was Assistant Professor in International Political Economy (IPE) at ESSCA in Paris, Adjunct Lecturer at Queen Elisabeth House at the University of Oxford, postdoctoral Research Fellow at LSE and Associate Lecturer at Oxford Brookes University, where he obtained his PhD in IPE. He also holds a MA in IPE from the University of Manchester. He has been a Visiting Research Fellow at the Institute of International Relations (Pontificia Universidade Catolica – PUC of Rio de Janeiro), the Institute of World Economics and Politics (IWEP) at the Chinese Academy of Social Sciences in Beijing, the Mercator Institute for China Studies (MERICS) in Berlin and the College of Business at Alfaisal University in Riyadh. He is the co-founder and coordinator of the European Think Tank Network of China (ETNC).
Source: This article was published by Elcano Royal Institute