Understanding The Danger Of Weapons Of Mass Destruction – Analysis
Introduction
The modern world is experiencing continued advancement in technology, which has created more room for organized criminal actions such as terrorism, human trafficking, smuggling, and money laundering (Mauroni, 2010). For instance, technology has facilitated the rapid development of robust emerging global networks that provide hostile non-state actors with a platform to share information on gaining access to destructive technologies. Weapons of Mass Destruction are hazardous as they can cause widespread devastation and loss of life (Archer, 2004). The WMDs are the greatest threat to public safety and instill fear in the world citizens.
Ideally, technology provides an easy avenue for non-state actors and other criminal organizations to manufacture and use WMD to inflict harm on innocent people. As such, the WMD presence in the hands of hostile power such as terrorists, rebels, or religious extremists is considered a grievous threat. The technological advancements are the reasons for developing more advanced WMDs such as biological, nuclear, radiological, and chemical weapons (Tibbetts 2002). The security organizations, such as Homeland Security, are working around the clock to prevent terrorists from accessing the weapons. Accordingly, there is a need to evaluate technology’s threat in enhancing the ease of use and access to mass destruction weapons.
Analysis
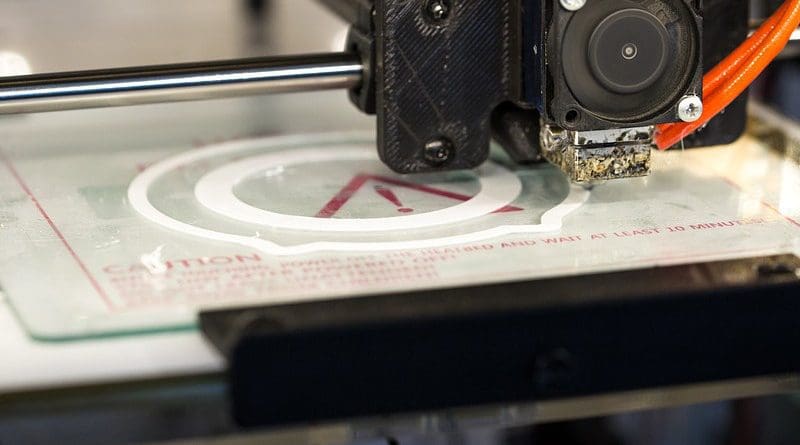
The United Nations Security Council recognizes that rapid technological advancements have created many opportunities for WMDs’ development and delivery systems (Mauroni, A. (2010). Such events pose a threat to numerous states of the world, such as the US. Various technological tools, such as dark websites, drones, 3D printing, etc., have continued to gain traction in the international security community, increasing threats to humanity.
3D printing was developed in the 1980s and has seen significant improvement in its multitude of functions (Vičar & Vičar, 2011). The 3D printers are relatively inexpensive; hence, they can be purchased or accessed easily. Most industries rely on printers to produce a myriad of identical parts. Economically, the printers facilitate repetitive operations and the making of detailed architectural design models. However, 3D technology can be applied in planning and manufacturing weapons like plastic firearms, which are hardly detectable in traditional airport scanners.
Alternatively, 3D printing can be involved in the planning, manufacturing, and transportation of WMDs and related prototypes. Engineers apply 3D printing in designing trial parts and study dimensions. For instance, 3D printing can be used to produce a complete model of a nuclear warhead. In the 1990s, the United States applied the technology in creating nuclear models that were used to train people on how to assemble and disassemble nuclear components for easy transportation (Tibbetts, 2002). 3D printing is inexpensive; it can be utilized in the printing of individual parts of weapons. It is cheap; hence, it provides an affordable alternative for hostile groups to create castings used in holding explosives, chemicals, or fissile materials for producing weapons. Additionally, the 3D printer can be used in manufacturing highly sought-after valves, fittings, and gauges for measuring pressure on weapons. 3D also helps in reconstructing damaged weapons; this can provide an opportunity for terrorists to collect damaged weapons in the battlefields for reconstruction and future use.
Similarly, dark websites enhance the potential of terrorists to access and manufacture WMDs. According to Bergen, Hoffman, and Tiedemann (2011), there is a deluge of weapons and technology available for purchase in various dark web markets. Thus, the websites enhance the potential of terrorists and other hostile organizations like Islamic extremists to access dangerous WMDs (Tibbetts, 2002). The dark websites provide underground marketplaces or criminal hotspots for hiring and purchasing illegal commodities. If not controlled, the site might facilitate terrorist access to WMDs.
Although the terrorist groups have a long way to go and still have substantial technical challenges to overcome in obtaining and using WMD, at the same time, the advancement in technologies could facilitate and this quest to materialize sooner and not later. Many terrorist groups and non-state actors explore the utilization of what is known as the Deep Web, referring to all encrypted web pages that traditional search engines or web browsers cannot find due to Tor encryption. They use Deep Web to search for means to manufacture and deliver WMD to their intended target. Nearly all the websites on the Deep Web use Tor encryption mechanisms to hide their identity and activities. For instance, a person can use Tor to parody his location. Subsequently, it looks the person is in a different nation than where he is actually located, just like in the same manner when we use a VPN service. The terrorist groups understand how to operate within closed-circuit, just like many secret organizations and societies can use the Deep Web to connect within as well as with the outside world. In addition to the Deep Web, terrorist groups and non-state actors’ use of drones and 3-D printers are rising apprehensions.
Drones, also products of technological innovations, have the potential for threats. Drones can be weaponized as militaries depend on drones’ versatility to hit targets that ground forces are unable to access. However, non-state actors or terrorists can use drones to covertly transport parts or whole of weapons from one location to another (O’Neil, 2003). Such an incident would make it difficult for security personnel or organizations to intercept and stop the terrorists from launching the deadly attacks.
Homeland Security organizations must be wary of the threats caused by dual-used technological items such as drones and 3D Printing innovation (Ellis, 2014). The Security Council finds itself in the dilemma of regulating their (drones & 3D printing) use without restricting the technologies’ legitimate purpose. Drones have a legitimate use as militaries depend on them to their targets that cannot be accessed by ground soldiers. Today, 3D technology is also too expedient to restrict its usage. However, drones and 3D technologies are extremely dangerous if accessible to terrorists and other actors of malice in the dark websites. The internet is full of videos showcasing how 3D facilitates the creation of plastic knives and guns. 3D and drones have both legitimate and illegitimate uses make it challenging to prevent WDMs from falling into the hands of hostile criminals and terrorists. Terrorists now take advantage of dual-use technologies to access, create, source, or transport weapons of mass destruction (Danzig, 2012). In 2015, Islamic Jihadists used mustard gas on civilians in Marea, Syria, leading to many deaths and causalities. The incident is an indication that terrorists are having access to WDMs.
Summary and Conclusion
In summary, therefore, technology is making terrorism to change in ways that will eventually be dangerous and difficult to combat (Vičar & Viča, 2011). There is a need for more security enhancement to prevent emerging security threats in the world. More so, the global chemical industry must take immediate measures to tighten the security of sensitive chemicals. The international community must unite and cooperate in fighting against terrorism and sealing all loopholes that would enhance terrorists’ access to WMDs.
*Dr. Mustapha Kulungu is the Principal Researcher at the ILM Foundation Institute of Los Angeles, California. He graduated from Fielding Graduate University, Santa Barbara, California.
References
Archer, T. A. (2004). The emperor has some clothes on fairy tales, scary tales, and Weapons of Mass Destruction.
Bergen, P., Hoffman, B., & Tiedemann, K. (2011). Assessing the Jihadist terrorist threat to America and American interests. Studies in Conflict & Terrorism, 34(2), 65-101.
Danzig, R. (2012). Innovation, dual-use, and security: managing the risks of emerging biological and chemical technologies. MIT press.
Ellis, P. (2014). Lone wolf terrorism and weapons of mass destruction: An examination of capabilities and countermeasures. Terrorism and Political Violence, 26.
Mauroni, A. (2010). Homeland Insecurity: Thinking About CBRN Terrorism. The Journal of the Naval Postgraduate School Center for Homeland Defense and Security, 7(3).
O’Neil, A. (2003). Terrorist use of weapons of mass destruction: how serious is the threat? Australian Journal of International Affairs, 57(1), 99-112.
Tibbetts, P. S. (2002). Terrorist Use of the Internet and Related Information Technologies. ARMY COMMAND AND GENERAL STAFF COLL FORT LEAVENWORTH KS SCHOOL OF ADVANCED MILITARY STUDIES.
Vičar, R., & Vičar, D. (2011). CBRN terrorism: A contribution to the analysis of risks. Journal of Defense Resources Management, 2, 21-28.